One thing I have learnt is you cannot have too many log files. If you want visibility into what is running commands on your server or who is running commands or what is executing, you need to enable PowerShell logging.
You get some really sophisticated malware that embeds itself in Windows and one way to get an idea of what is going on is to look at the PowerShell logs in Event Viewer, not only will this give you the command run but it should also list the IP address where it is calling home.
To enable this, you can set PowerShell logging with Group Policy or you can enable a registry key as follows:
- HKEY_LOCAL_MACHINE \SOFTWARE\ Policies\Microsoft\Windows\PowerShell\ScriptBlockLogging\
and create a DWord called “EnableScriptBlockLogging” with a value of 1.
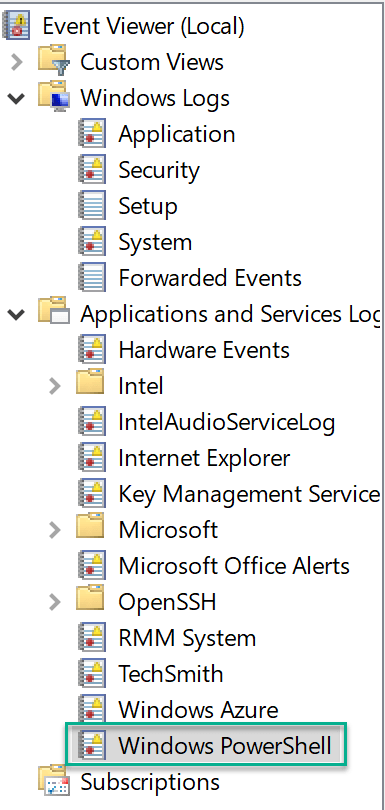
Once you had done either of the options, you can head over to the Event Viewer and expand “Applications and Services Log, you will see “Windows PowerShell” where you can now view all the event:
There are many logs in here but you will pick up things pretty quickly once you start sifting through it. What does work if you export the Windows PowerShell log file and then open it in Notepad++ and then look for information.
Hope it helps.
