Many items that run in Windows have scheduled tasks that run at certain intervals. Malware and bad actors like abusing scheduled tasks because they contain elevated privileged accounts which run as SYSTEM. Have you ever wondered what is actually running on Windows Server, for example, Windows Server 2022?
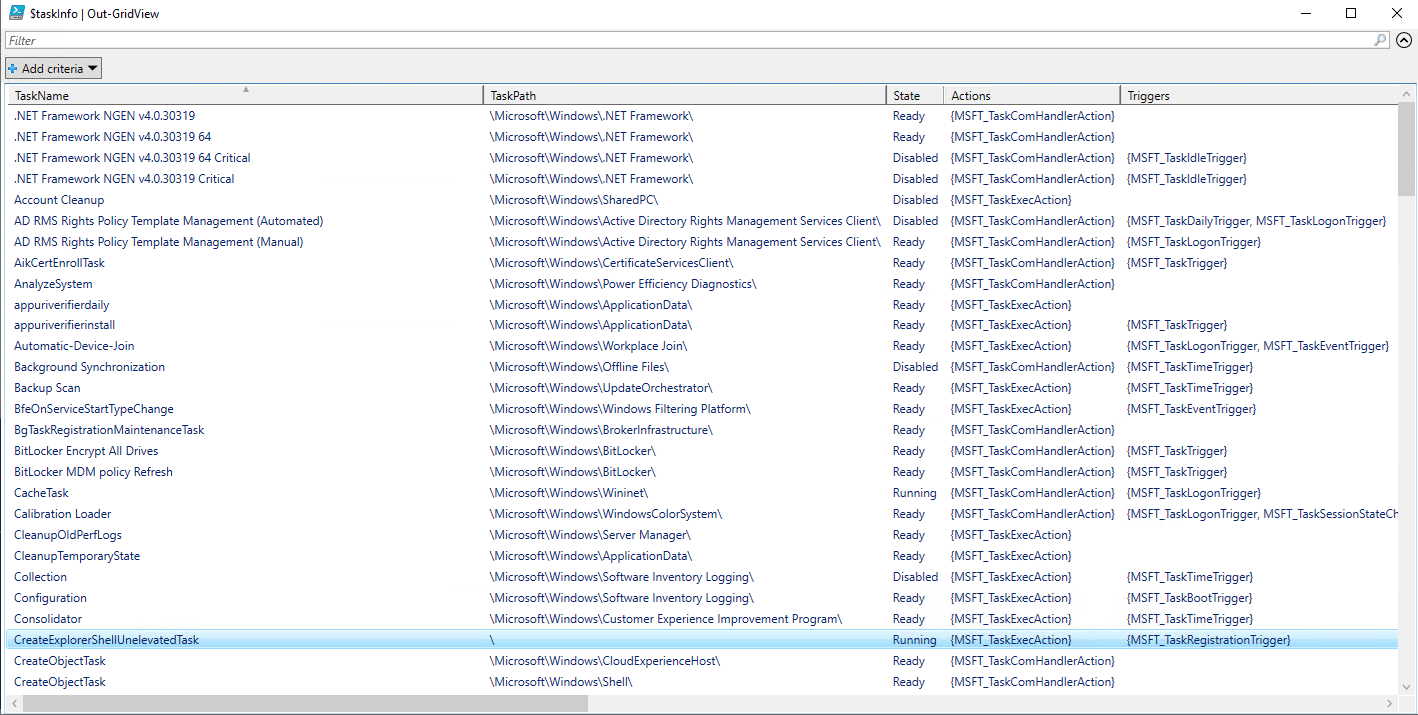
In my lab I wanted to see what was running from a single pane instead of going through each folder to see what tasks are running. You can see a snippet below where I ran a script that gives you all the information in a Grid layout because it’s clean and readable.
You may be wondering why should I be doing this? Many times admins setup scheduled tasks with domain admin or accounts with more privileges because they don’t want the hassle of it not working but forget that there credentials are now stored and if the system is penetrated by a bad actor, one of the first place they will look at is the scheduled tasks.
To add to this, if a bad actor does get the credentials of an elevated account, they could use Task Scheduler to setup a backdoor that is always available and you will be none the wiser because your account was used to set it up and run whatever they want to run with full system privileges. Below is a snippet of the output in PowerShell and the Grid.
SCRIPT
To get the information above, I put together a simple PowerShell script, feel free to add to it if you want specific information to show:
# Get all scheduled tasks, including hidden ones
$scheduledTasks = Get-ScheduledTask
# Select relevant properties for display
$taskInfo = $scheduledTasks | Select-Object TaskName, TaskPath, State, Actions, Triggers, Principal, Description, Status
# Export the information to a grid view
$taskInfo | Out-GridViewThe script does not take long to run on a machine, you could always add a variable to specify computer names and then run a for loop against that.
Hope it helps.
